SpotLightTM/SpotLightTM Duo Cyber Security Policy

Revision History
| Revision | Date | Reason for Change |
|---|---|---|
| 1.00 | 02-Oct 2023 | initial revision for SpotLight – create a revision identical to CardioGraphe Cyber Security Policy, without CE Mark |
Table of Contents
1. TABLE OF CONTENTS
2. OVERVIEW
3. DEFINITIONS
• ACRONYMS AND ABBREVIATIONS
• REFERENCES
4. PRODUCT MANUFACTURER
5. STRATEGIC APPROACH
6. DESIGN FOR SECURITY
7. CUSTOMER SECURITY PARTNERSHIP
• REMOTE SERVICE
• PAY-PER-USE PROGRAM
• ANTI-VIRUS AS AN OPTIONAL PROTECTION
8. ONGOING SECURITY VIGILANCE
• OS SECURITY UPDATES
• SOUP AND 3RD PARTY COMPONENTS
• MDS2 FORM
Overview
This paper applies to SpotLight/SpotLight DUO CT CT system and presents Arineta policy in addressing the cybersecurity risks from the product perspective. Throughout the document, where mentioning SpotLight – the intention is for SpotLight and SpotLight Duo products (two products totally equivalent beside the detection unit that do not have any relation/effect on Cyber Security of the system).
Cybersecurity is not a one-time solution nor a one-time event. The effective approach to address the cybersecurity challenges of medical device is a framework and a partnership.
The framework includes a clear approach to secure SpotLight by design and continuous vigilance. The partnership is the collaboration with the customer and Arienta’s service to enhance the security of SpotLight on site.
Definitions
• Acronyms and Abbreviations
CT – Computed Tomography
DICOM – Digital Imaging and Communications in Medicine
OS – Operating System
ISO – International Organization for Standards
SOUP – Software of unknown (or uncertain) pedigree (or provenance)
OTS – Off the shelf software
AV – Anti Virus
• References
FDA – “Postmarket Management of Cybersecurity in Medical Devices”, Dec 28, 2016
FDA – “Premarket Submissions for Management of Cybersecurity in Medical Devices”, Draft
Guidance, Oct, 18, 2018
MDR – “Guidance on Cybersecurity for medical devices”, MDCG 2019-16, Dec, 2019
MDS2 – “Manufacturer Disclosure Statement for Medical Device Security” form, ANSI/NEMA
HN 1-2019
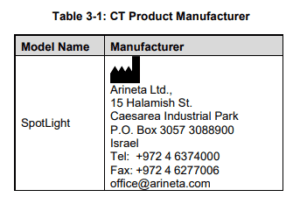
Product manufacturer
Strategic approach
Arineta applies design for security in SpotLight, as well as risk assessment and incident
response activities in case vulnerability is identified.
Our strategic approach aspects assure the product safety and performance needs as well as controlled and secure integration with the site infrastructure:
- Design for security
- Customer security partnership
- Ongoing security vigilance
Design for security
The cybersecurity framework core functions guide the risk analysis and the design concepts: Identify, Protect, Detect, Respond, and Recover.
SpotLight actively prevents malware intrusion to the device content, services and actions running on the device by taking the following key steps:
- SpotLight is a complex medical device with integrated 3rd party components (like Windows OS). Risk based approach is used by the Arineta engineering and only secured components are included in the product after complete verification cycle.
- SpotLight is a Windows OS based system. Hardened embedded OS image is configured only with essential services and components, thus reducing the penetration risks. This includes disabling of auto-updates.
- SpotLight device activation is limited to authenticated clinical operators and authorized service personnel. Any system access requires login with password and permissions are limited to the level of necessity. The clinical operators are managed by the site clinical administrator and can be reverted or even deleted.
- SpotLight eliminates USB automatic file execution which is viruses’ major way of penetrating the system. Whitelisting Control is a strong prevention tool and limits execution on the device only to the approved programs set.
- Build-in Windows Defender antispyware program is a part of the device OS. It is designed to prevent and detect unwanted spyware program installations and to remove those programs.
- Protection of the operating system partition by write protect filter prevents altering the OS settings and content by reverting any changes upon reboot. The device file system limits access and changes of files and directories according to the permissions level of Windows users.
- Windows firewall rules prevent all Inbound connections except for essential services:
ICMP (ping); SNMP (network management). - Windows firewall Outbound connection rules limit access only to SpotLight workflow partners
• Interoperability with modality worklist devices (HIS/RIS)
• DICOM records transfer to SCP devices (PACS, Workstations)
• Connection via secured GE enterprise tunnel for remote servicing
• Connection of preregistered devices via secured Arineta tunnel for reporting of billable usage records.
Customer Security Partnership
SpotLight security is an important part of our development effort. However, protection can only be realized if the customer implements a comprehensive on-site cybersecurity approach, including policies, processes, and technologies to protect information and systems from external and internal threats.
- The SpotLight device activation is limited to authenticated clinical operators and authorized service personnel. Only trained and certified Arineta service providers should have access to the device.
- Installation of 3 rd party software including off-the-shelf products (e.g., virus scanners, office productivity tools, OS patches) by the customer without prior written consent by Arineta is prohibited. Unauthorized modifications to the device can void warranty, alter the regulatory status of the device and can adversely affect the performance, functionality or safety of SpotLight in unpredictable ways.
• Remote Service
SpotLight supports controlled remote services via Arineta infrastructure and by Arineta service personnel. This design provides Arineta service with a single point of network access to SpotLight system using web technologies. This secured tunnel approach is initiated only by the device with explicit authentication mechanism to specific predefined
Arineta domain server. The whole service session is based on encrypted data exchange.
• Pay-Per-Use program
SpotLight offers customers a Pay-Per-Use billing model. Scanners participating in this program initiate restricted, secured single communication channel to Arineta billing service.
This secured tunnel approach is initiated only by the device with explicit authentication mechanism to specific predefined Arineta domain server.
The session is based on encrypted anonymized data exchange per region.
• Anti-Virus as an optional protection
Note that AV has impact on the device performance and even functionality. It also opens the inbound ports for updates and raises the penetration risk.
Prior to installing of AV on SpotLight, customer shall contact Arineta service representative to determine if particular AV has been qualified for SpotLight and, if so, what restrictions may apply
Ongoing security vigilance
Arineta uses treat modeling as an ongoing risk management process to identify and address possible cybersecurity risks. The team is engaged in monitoring sources for new risks like customer complaints, cybersecurity forums, software development communities and medical device industry publications. The risks are assessed for relevance and risk level. Recommendations and actions are translated into corrective and preventive changes, for released products and product under development.
• OS Security Updates
SpotLight system is based on embedded Microsoft Windows OS. Arineta analyzes the impact of MS Windows security updates on SpotLight. If the recommended response requires a change on SpotLight, a software update may be released.
• SOUP and 3rd party components
The engineering team examines the usage of 3rd party software as part of the design phases. Incorporation of these components in the product are analyzed before inclusion and afterwards to monitor newly identified security risks and offered remedies.
• MDS2 Form
Arineta maintains “Manufacturer Disclosure Statement for Medical Device Security” (MDS2) form to assist healthcare providers in managing the vulnerabilities and risks associated with electronic protected health.
![]()
Arineta Ltd.
15 Halamish St. Caesarea Industrial Park North 3088900 Israel
© 2015 Arineta Ltd. All Rights Reserved.


